It happened again. Once again another security issue has slipped through the cracks, only to be discovered 23 years later…
Dang, that’s a long time.
Coming to light this week is the Meltdown and Spectre vulnerabilities. And it has nothing to do with James Bond, though along the same lines I suppose.
These vulnerabilities are in the design of the CPU and RAM of a computer, and have been built into nearly most every computer built since 1995. They are hardware bugs, not software, so they are harder to fix.
Let the Meltdown Begin
Let’s see what happened. First up is Meltdown, which mainly effects Intel chips. It allows malicious programs to read the memory of other good, secure programs. It’s not the fault of the good programs, but rather in how the chip processes data before checking if it actually should (to speed up performance).
Here’s a 14 second video showing how it does so. The top box is the password manager. The bottom part is the malicious program reading/spying on the memory of the good program.
In the Cloud, this attack can effect Xen and other software based solutions. KVM and other true hypervisors are (as of yet) not believed to be effected.
Not Your Average Spectre
Spectre on the other hand tricks other programs into leaking their secrets, by utilizing memory performance enhancements in bad ways. It’s tougher to exploit, but it’s still bad.
And it can be exploited in JavaScript. Yes, the websites that you visit may be able to exploit it. Some browsers have mitigations for it. In Chrome you can turn on Site Isolation by going to chrome://flags#enable-site-per-process and Enabling it. Or in Firefox go to about:config and set privacy.firstparty.isolate to true. Both of those browsers are planning to release mitigated versions soon.
As for the Cloud, they are all effected by this attack, because it can effect the hypervisor. So it’s best to see what your cloud company is doing about it. Otherwise:
Yes, I just had to make a 007 Spectre reference here. And it fits: single little issue takes down entire main operation.
Though I personally prefer the non-violent tactics of Bourne…
What can I do? Should I worry?
There are many patches that have already come out, and others on the way. So update your system, bios, etc as soon as you can.
The exploits leave no trace. That’s the really bad thing about it. Some say they would be more useful for “targeted” victims. But it’s hard to say at this point. Probably best to update your systems, and bios, and then to change your passwords.
The sad part was that the vulnerabilities became publicly known before all the patches had been released. So it may have given time for exploits to be made and used before the patches came out.
Conclusion
I still find it odd that both of these exploits have to do with things that were related to increasing performance. Yet another “feature” that could have been more appropriately described as a “waiting security bug”.
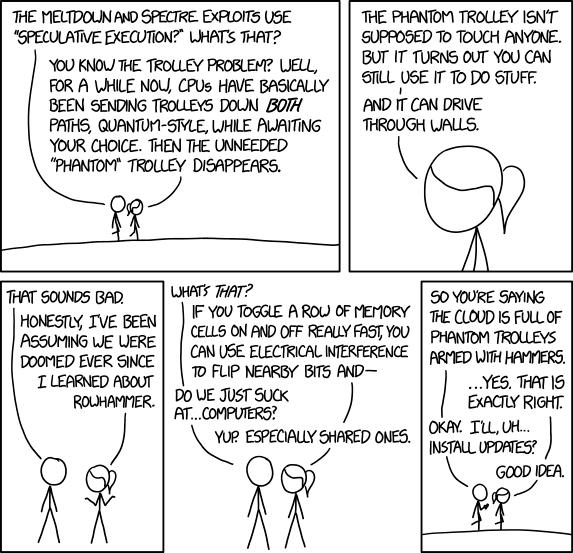
But on a good note, here’s a comic:
Meltdown and Spectre comic by xkcd